Hello friend,
How are you? I hope you’re having a joyful summer.
Do you know what it’s like when you’re used to perceiving certain concepts in a particular way, but when you simply change your lens, a much clearer perspective emerges?
Try this!
What’s the first thing that comes to your mind when you think about “cybersecurity threats?”
If you’re thinking about a wide range of harm-driven cyber attacks ranging from phishing, malware, and identity-based, ransomware to AI deepfakes - you’re of course correct.
Yesterday, changing lens, it dawned on me that all these malicious attacks in essence use tactics to mislead and fool people by leveraging the power of story and impact of visuals.
How so?
A targeted phishing email may concoct a believable story using your boss's name as the sender with a work-related story.
After a warm intro, it will switch to act 2: the conflict:
“I’m currently on the road so it would help me a lot if in the meantime you could forward $500 to my travel expenses account and I’ll pay you back when I’m back…”
To make the story even more believable, some hackers may even use “visual credibility amplifiers” to tighten up the illusion, using your company’s email template, signature format, and logo.
Another classic of the genre, you may remember, is of course the Nigerian Prince phishing scam.
The formula included these narrative ingredients: A wealthy individual, appealing backstory, conflict, call-to-action, and disappearance.
From this perspective, all hackers are doing is, in essence, throwing “visual storytelling darts” at scale or on specific targets to trick the credulous.
Welcome to a new kind of “Visual Storyteller Fest” where grand prizes are awarded not by a literary judging committee but - sadly - by those who fall prey to those fake stories…
What is Cyber Crime?
“Damage and destruction of data, stolen money, lost productivity, theft of intellectual property, theft of personal and financial data, embezzlement, fraud, post-attack disruption to the normal course of business, forensic investigation, restoration and deletion of hacked data and systems, and reputational harm.”
- Cyber Crime Magazine
The stakes are high
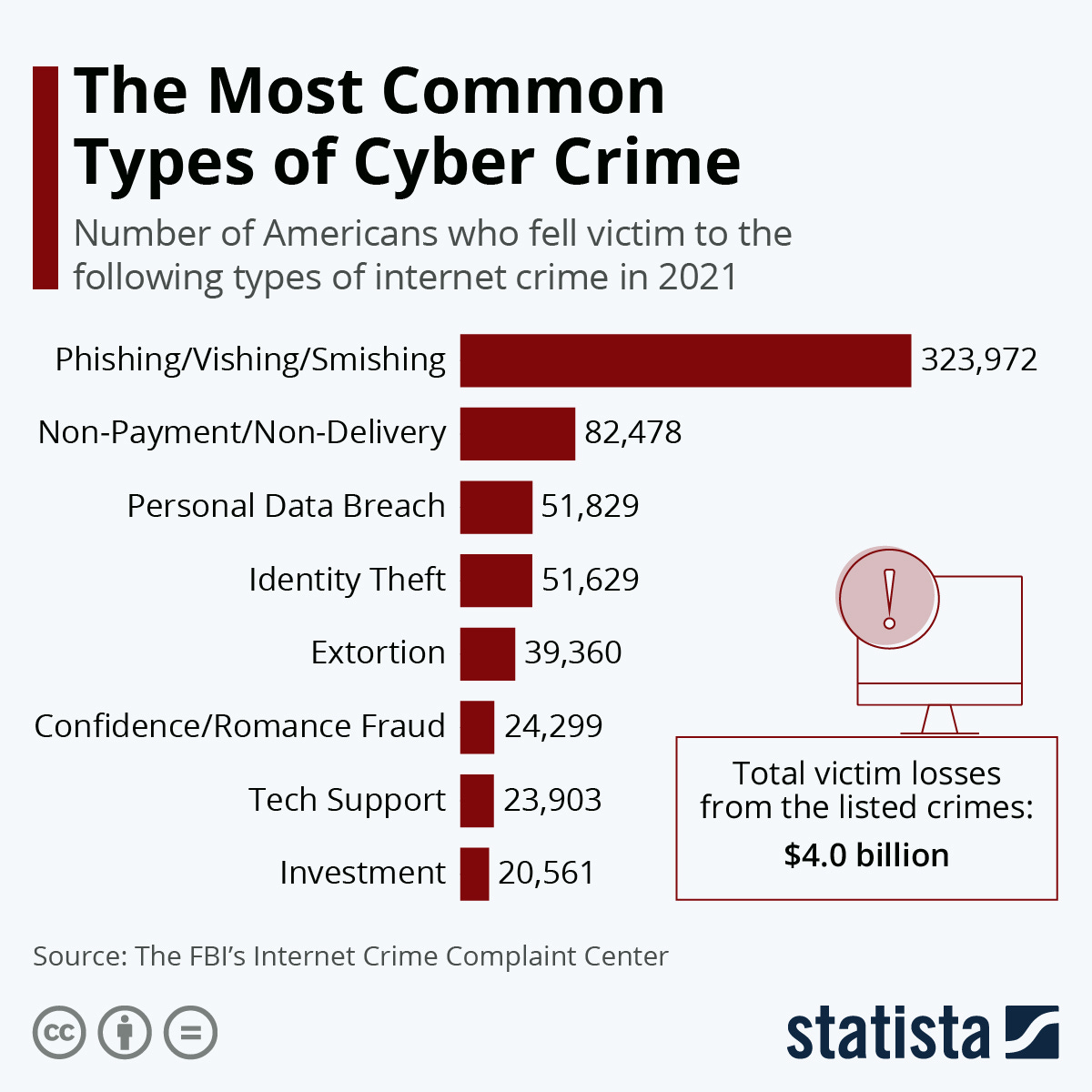
Cybercrime is a growing problem that affects individuals, companies, and countries.
The global cost of cybercrime is expected to balloon to $23.82 trillion U.S. dollars by 2027 (Statista). Yep! We’re talking trillions!
Think about the damage cybercrime can do.
From stealing, modifying, or destroying data, losing productivity, damaging brand reputation, and repair costs - up to state security breaches.
Since cyber incidents pose the highest risk for businesses and the fact that in essence hackers use visual storytelling to mislead, I figured this is worth digging deeper.

Meet the expert
Looking at cybercrime as visual storytelling harnessed for bad motives, I was intrigued about how cybersecurity companies can also use visual storytelling techniques, but for good - helping businesses before and after they get hit.
It has a lot to do with education, as often all it takes is for one employee to slip, clicking on a bogus link to shut down the company’s entire system.
To help me unpack this important topic, I had the pleasure to chat with Reginald Andre, founder and CEO of the Miami-based cybersecurity company, Ark Solvers.
Andre was recently featured as a 40 under 40 honoree award and as the Fastest Growing IT company in South FL 3 years in a row!
I met Andre at a recent meeting of Miami Tech Works, Tech Talent Coalition we both participated. It’s an industry-led, tech-sector partnership that brings together a critical mass of business leaders with education and training providers to align academic programs with the actual needs of the tech industry in South Florida.
In this podcast, we talked about his unusual journey into cybersecurity, his visual storytelling tactics to convey cybersecurity threats, his mind-boggling examples, his take on future AI cyber crime, his top 3 tips for using visual storytelling for high-stakes businesses, and much more.
It’s all in the latest episode of the Visual Storytelling Today podcast.
Watch the full video recording of this interview with lots of illustrative examples:
Need a screenbreak?
You can also listen to the audio recording of this episode. Subscribe to the Visual Storytelling Today podcast on iTunes, Google Podcasts, and all other podcast networks.
As you’re tuning in or watching our chat, think about what you can do to educate your team, and safeguard your workflows and systems to handle cyber attacks.
Preempting hackers’ fake stories before rather than after is always a better idea.
Until next time keep spreading stories that help improve people’s lives while celebrating your brand.
Best,
- Shlomi
Shlomi Ron
Founder & CEO | Visual Storytelling Institute
shlomi@visualstorytell.com | calendar
story > visual > emotion > experience